Overview:
EasyTerritory (version 3.x+) supports Azure Active Directory (Azure AD) using MSAL. Azure AD is a Single sign-on (SSO) feature that enables a user to login to the EasyTerritory application through Azure AD. Azure AD will authenticate the user using Active Directory credentials and direct them to EasyTerritory to access the application. Additionally, Azure AD at EasyTerritory v3 supports Advanced Find mapping results from a Dynamics 365 instance to EasyTerritory without the Dynamics 365 credentials prompt previously experienced in EasyTerritory v2.x and earlier.
Advantages:
The advantages of leveraging Azure AD with your EasyTerritory application are:
- Simple streamlined SSO access to your EasyTerritory application and Dynamics 365 instance through company’s Azure AD portal.
- Strengthens security with users not needing to remember additional usernames and passwords.
- Ability for companies to control users’ access to EasyTerritory within their Active Directory.
- End-to-end authentication for Dynamics 365 FetchXML layers (Advanced Find mapping).
- Supports multi-factor authentication (MFA).
Prerequisites
You will need to be an Office 365 admin and have access to the Microsoft Azure Portal for your organization.
Azure AD Configuration Steps:
-
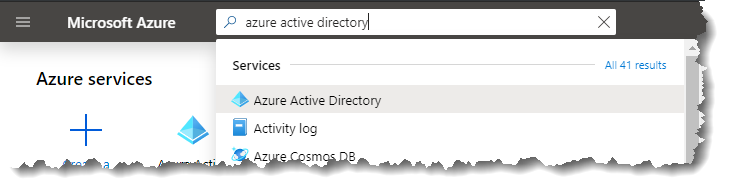
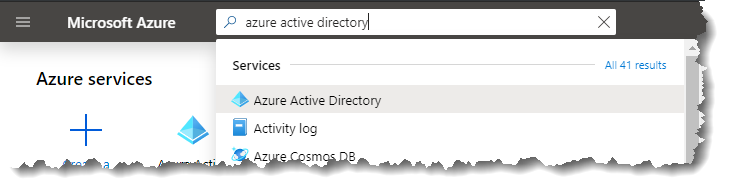
- Login to the Azure Portal (https://portal.azure.com) and click ‘Azure Active Directory’
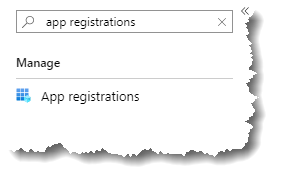
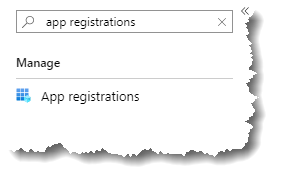
- Then select ‘App Registrations’
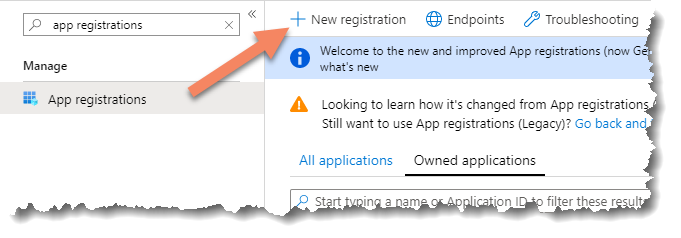
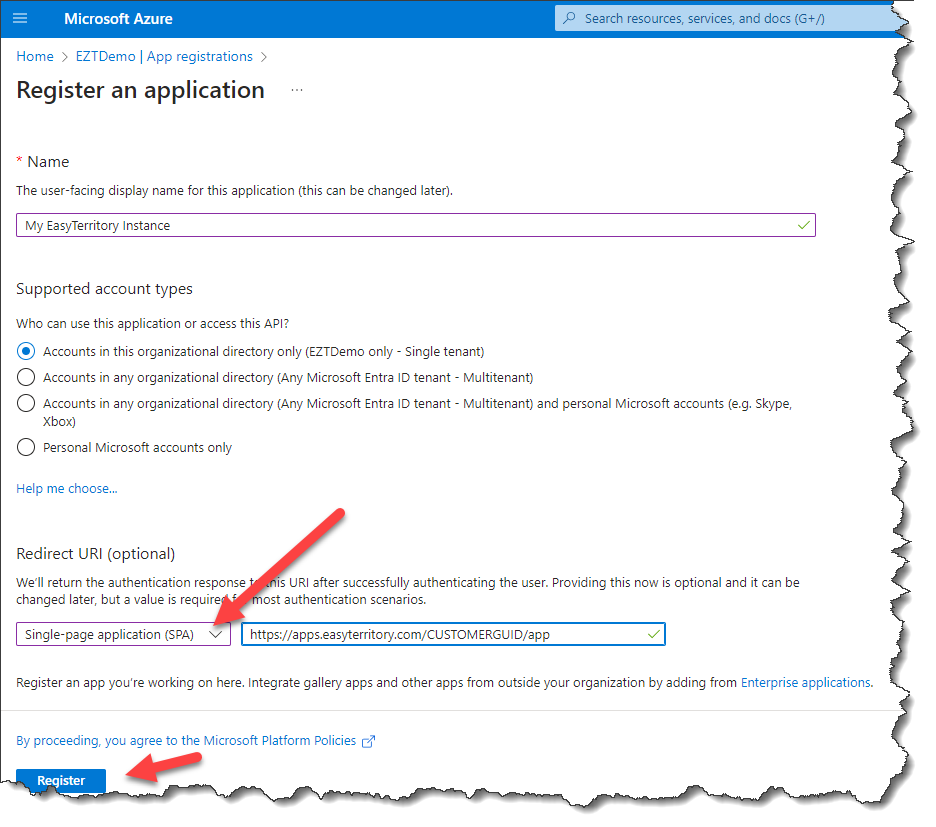
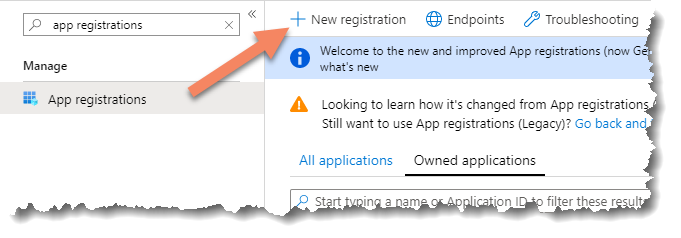
- Click ‘+ New application registration’
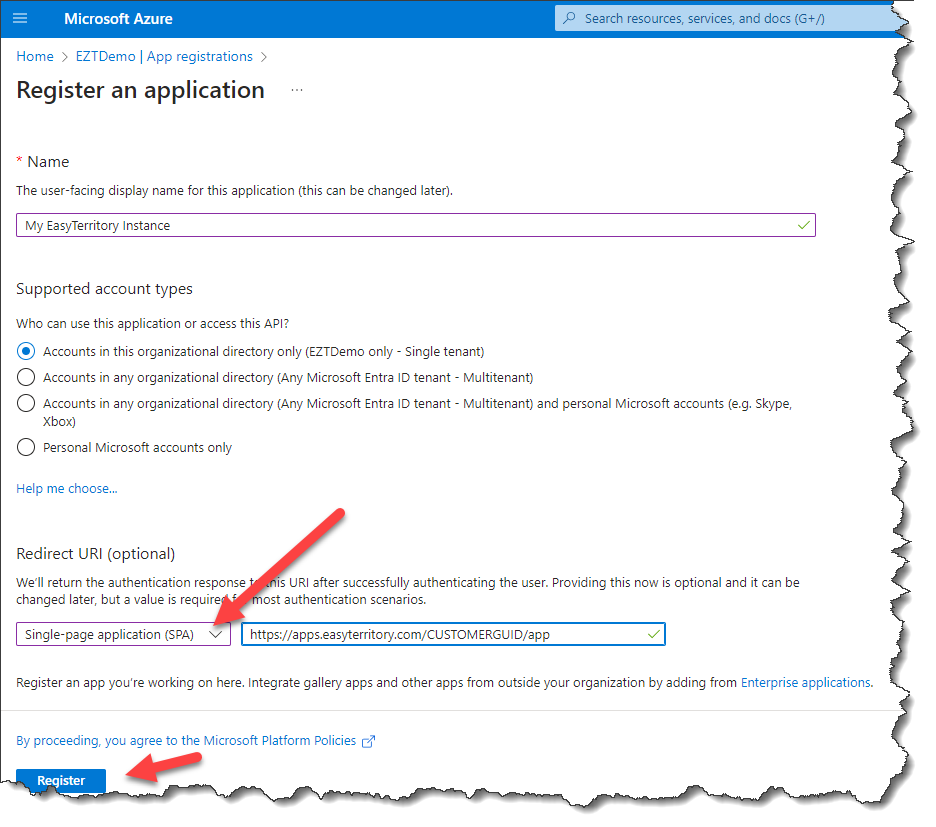
- Set a ‘Name’ for your configuration, Choose ‘Application type’ = Single-page Application (SPA), set your ‘Sign-on URL’ = ‘https://apps.easyterritory.com/GUID/app/’ (replacing GUID with your customer GUID). Click ‘Register’.
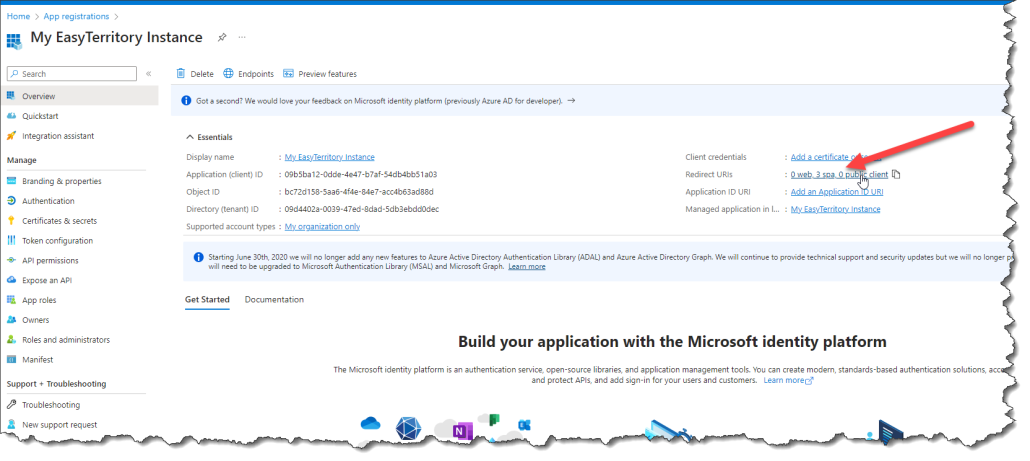
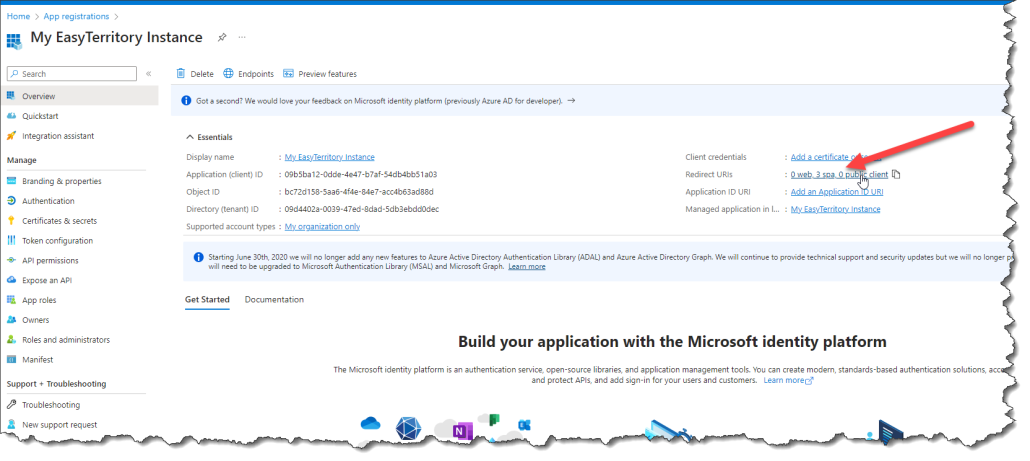
- Click ‘Overview’, then click ‘Redirect URIs’ in the panel that appear.
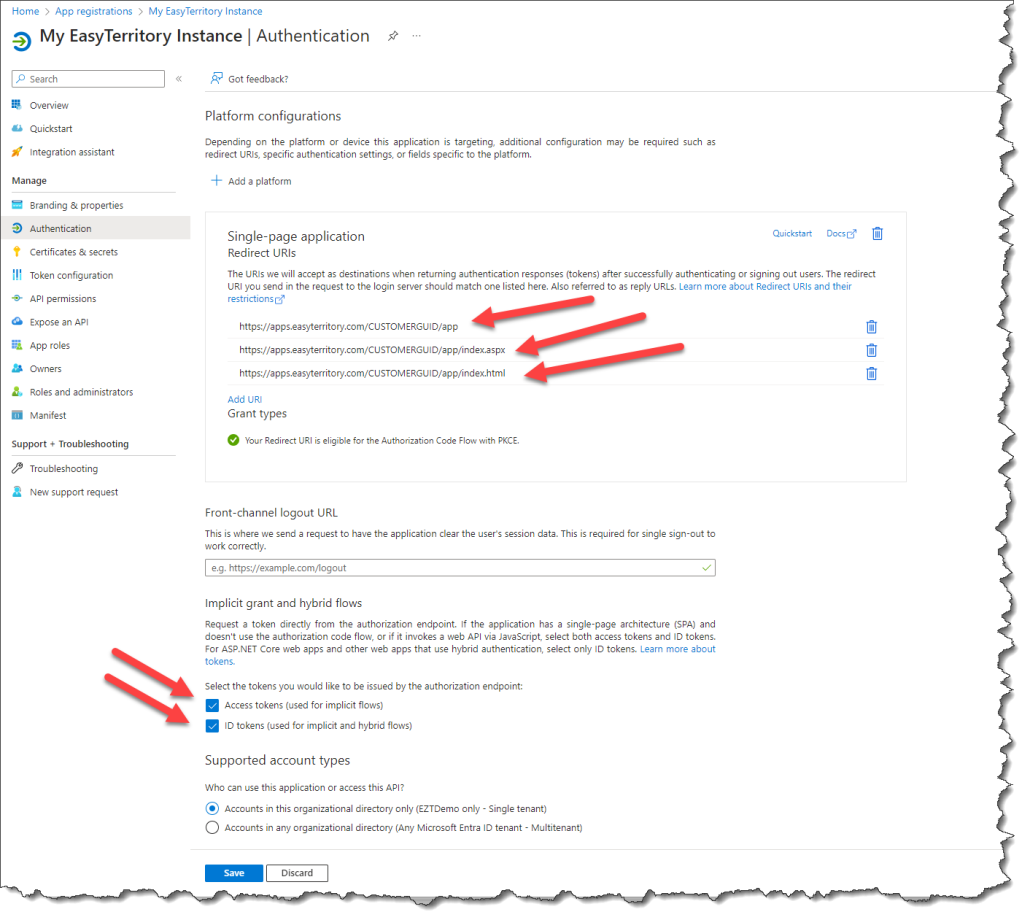
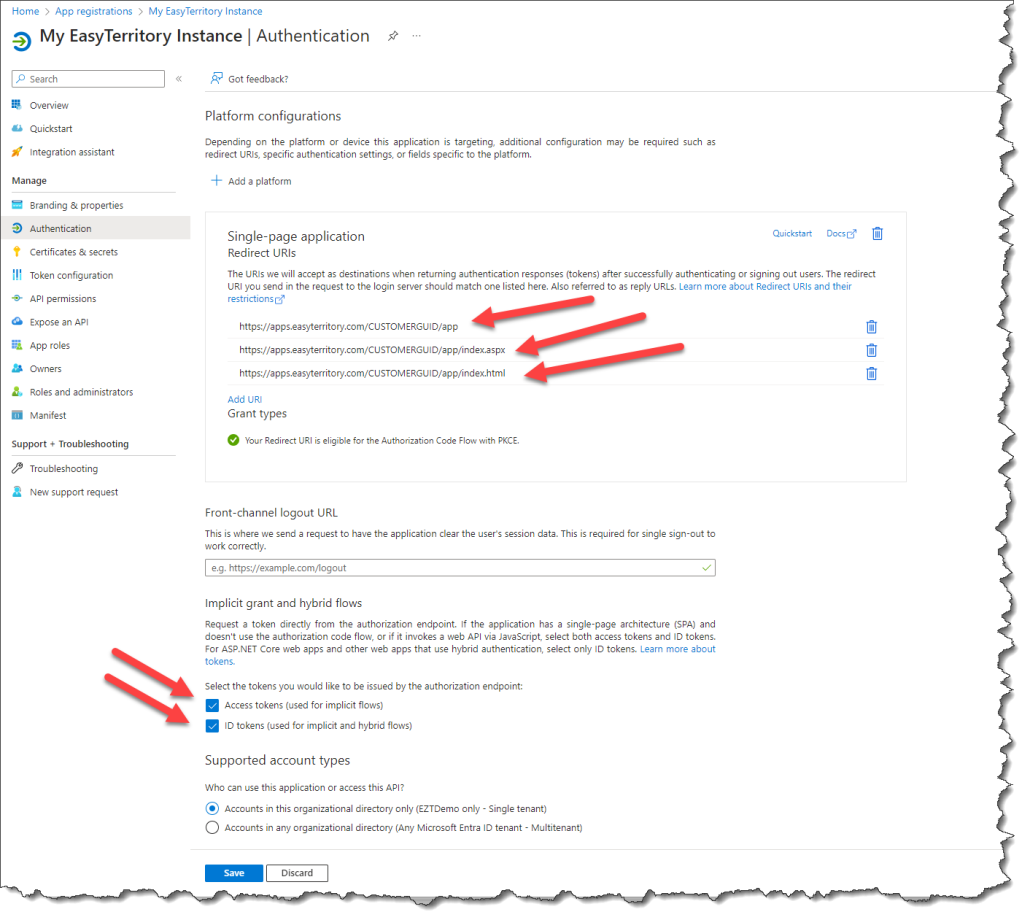
- Add the following three Redirect URIs (replacing GUID with your customer GUID and setting DEV/TEST/APP to correspond to your instance type. APP = PROD).
- https://apps.easyterritory.com/GUID/{DEV}{TEST}{APP}
- https://apps.easyterritory.com/GUID/{DEV}{TEST}{APP}/index.html
- https://apps.easyterritory.com/GUID/{DEV}{TEST}{APP}/index.aspx
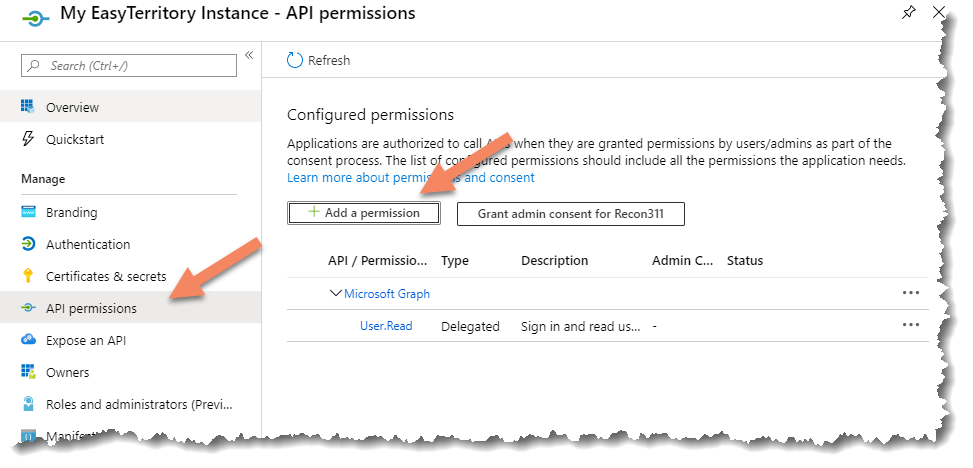
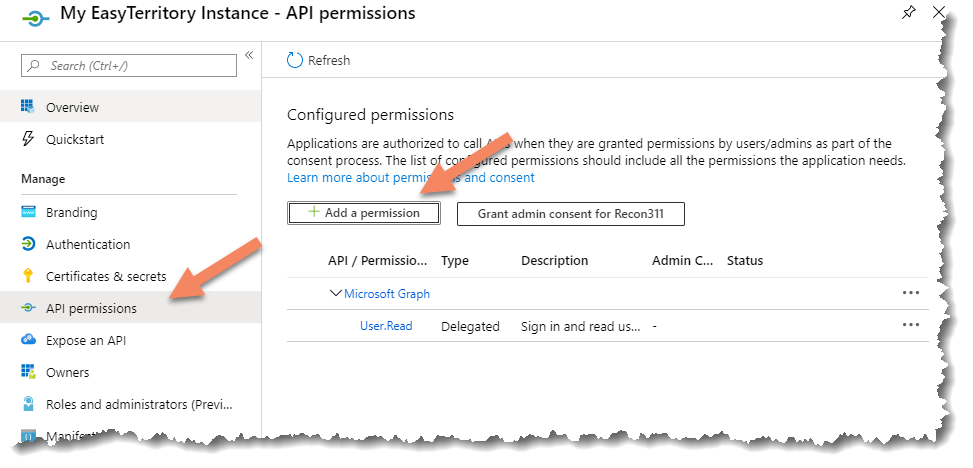
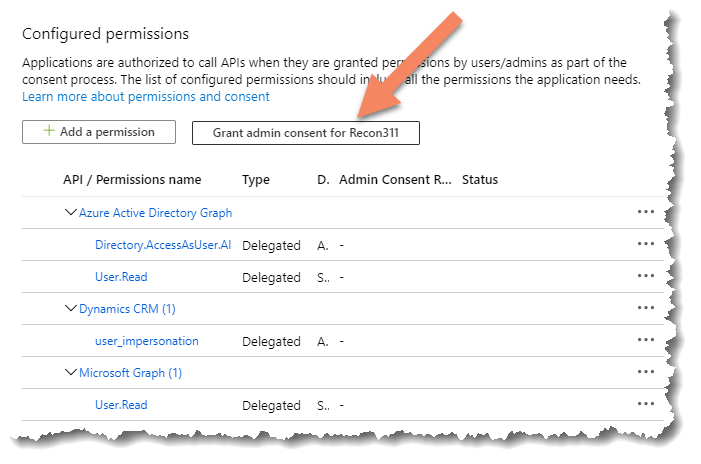
- Click ‘Add a permission’.
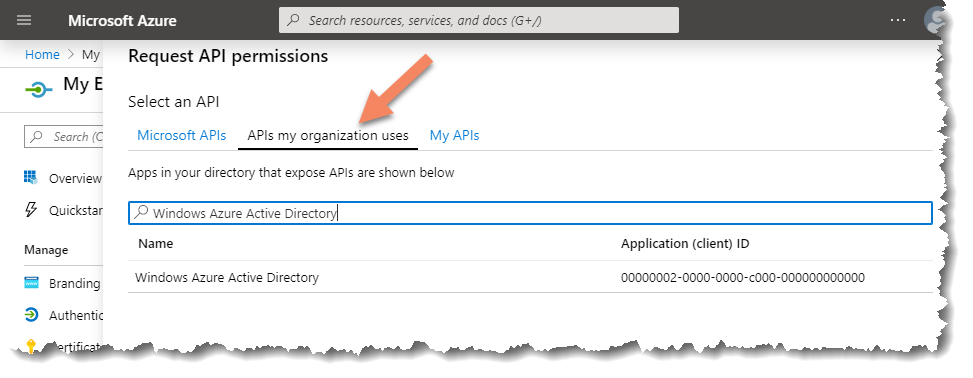
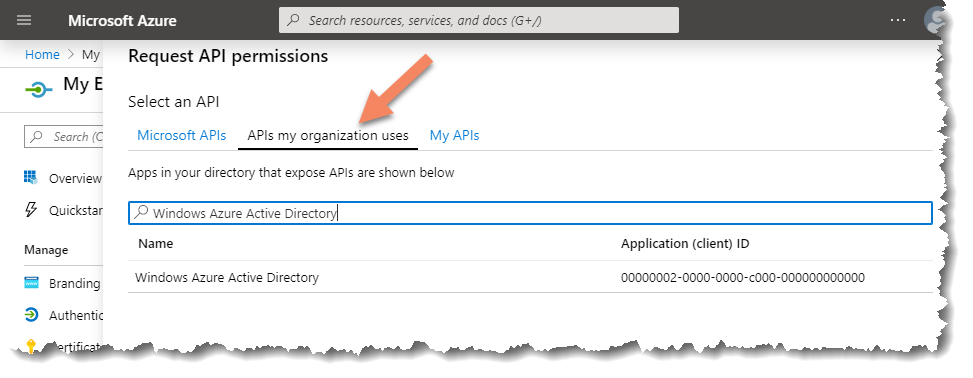
- Click the ‘APIs my organization uses’ tab and then type in the search box ‘Windows Azure Active Directory’. Click on ‘Windows Azure Active Directory’.
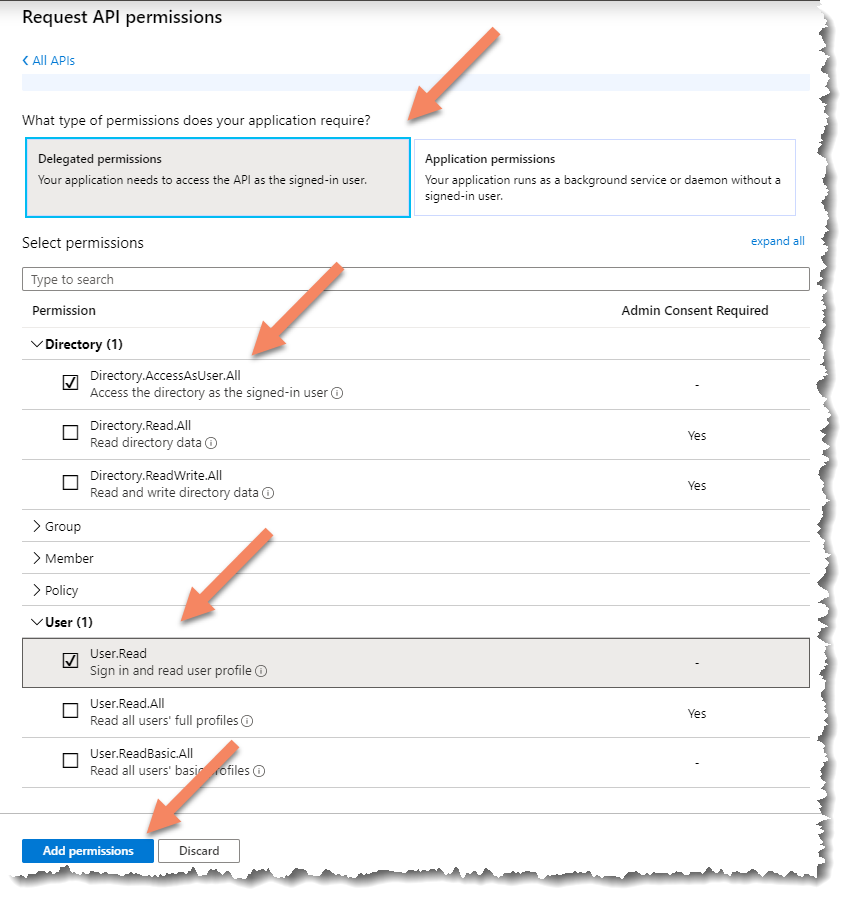
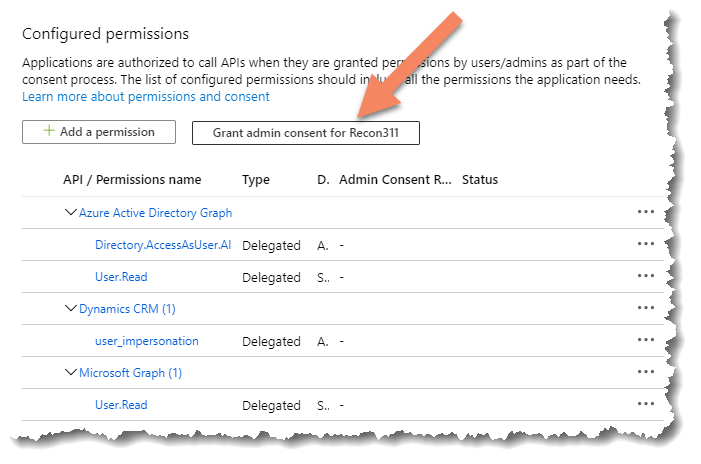
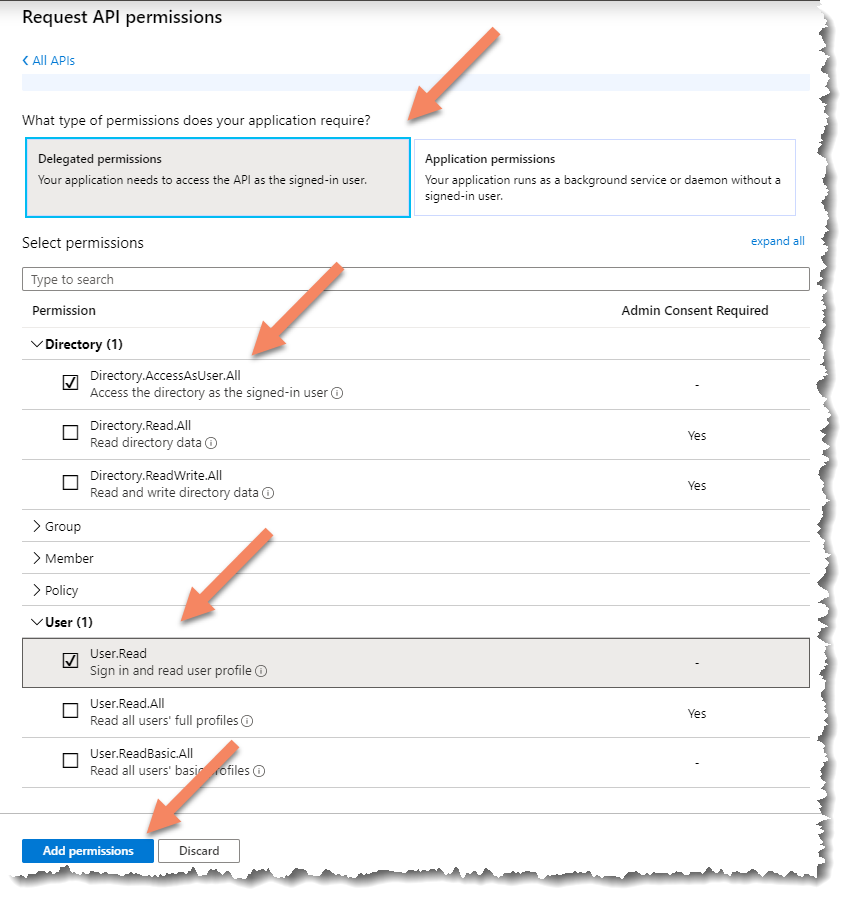
- Check the following delegated permissions and click ‘Add permissions’
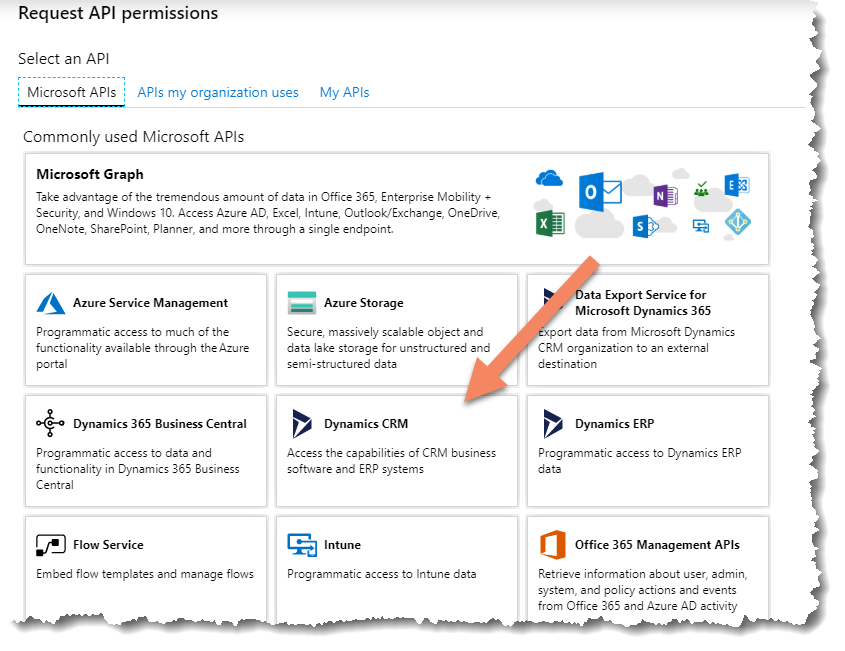
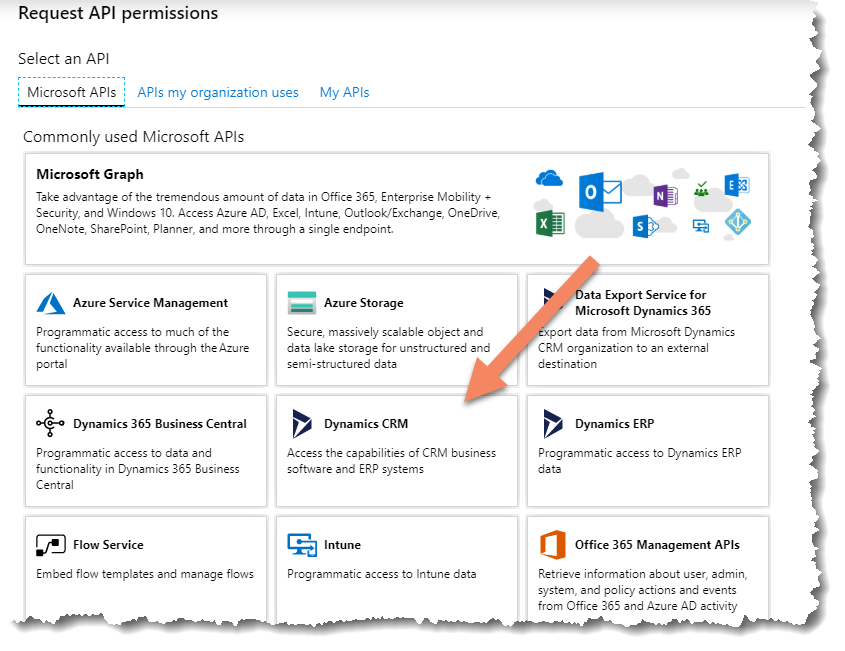
- OPTIONAL: If connecting to Dynamics 365, add access to the API. Click ‘+ Add’ then click ‘Select an API”. In the search box, search for ‘Dynamics CRM Online (Microsoft.CRM)’ and select it.
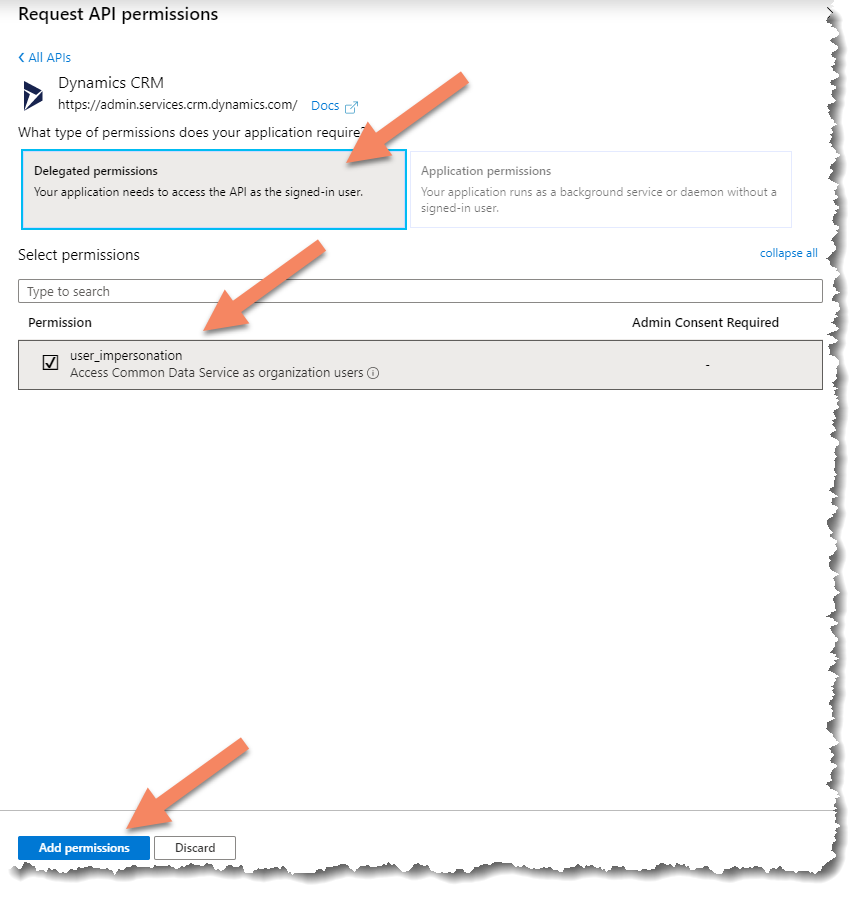
- Select the following delegated permissions and ‘Save’.
- Click ‘Grant Admin consent’
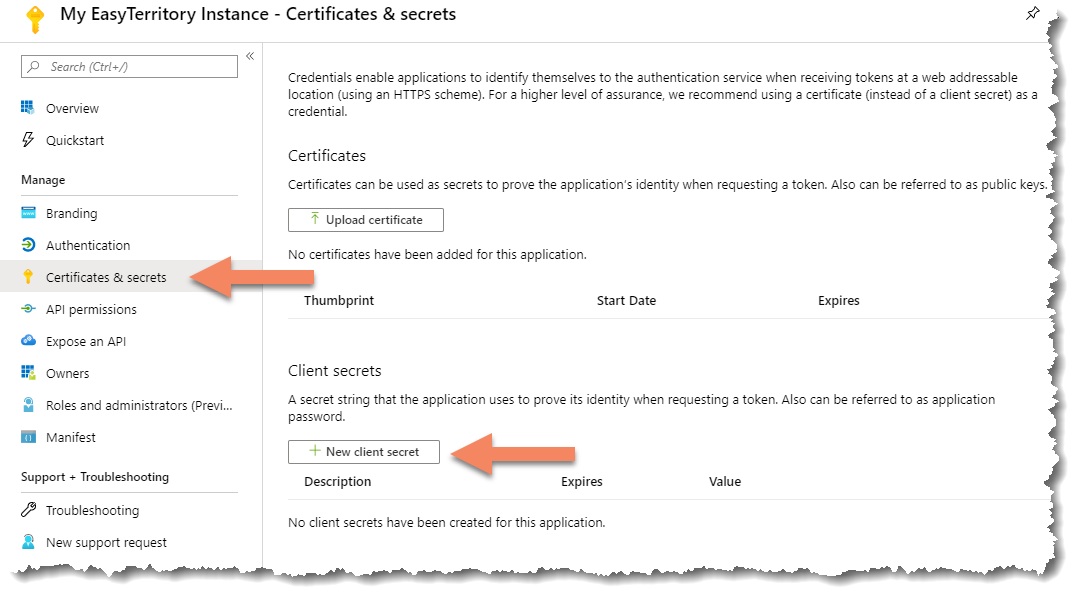
- Next, setup an Application Key. Note:
- You will need to copy it out as the UI will never let you get back to it after the blade closes.
- The Key will be pasted into an EasyTerritory setting on the last step.
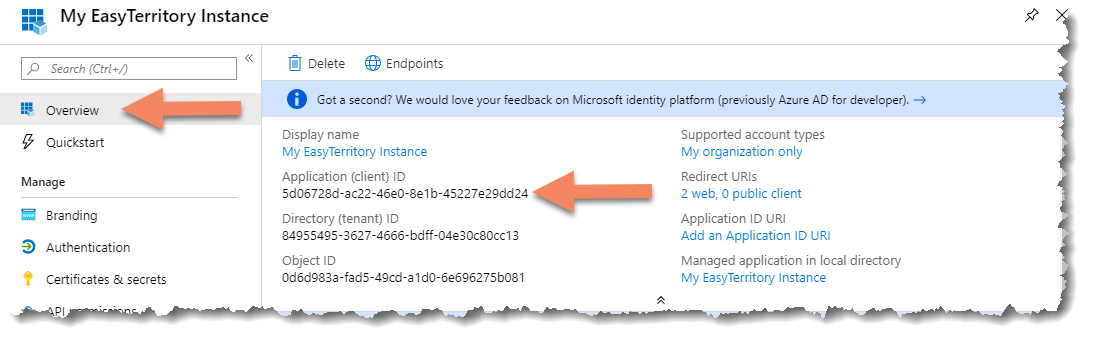
- Get the Application ID and OAuth endpoints for copying into the EasyTerritory settings panel.
- Get the Application ID here:
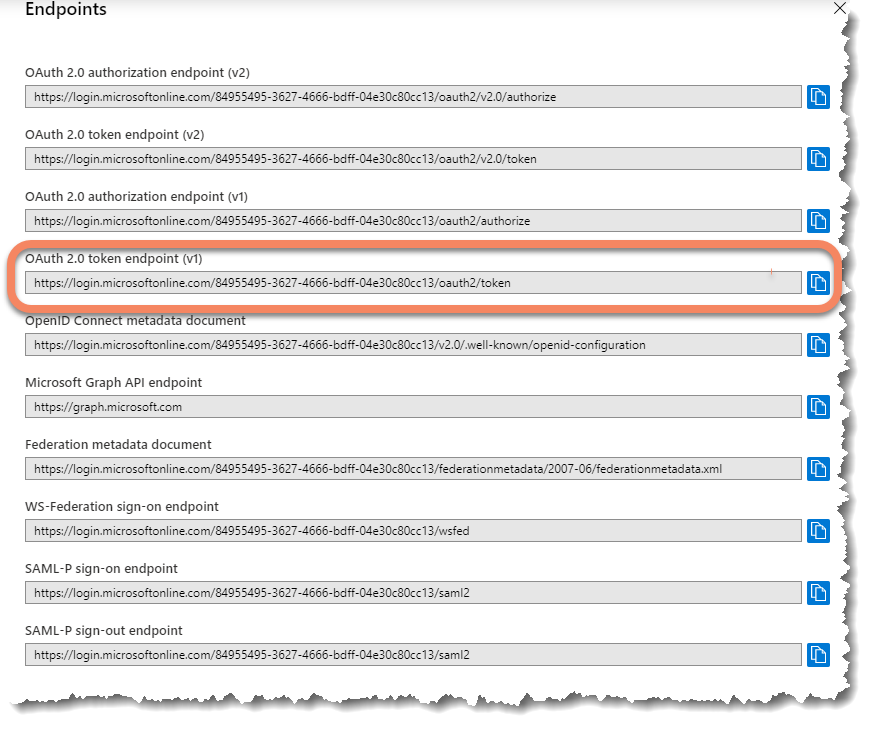
- Get the OAuth Endpoint by clicking here:
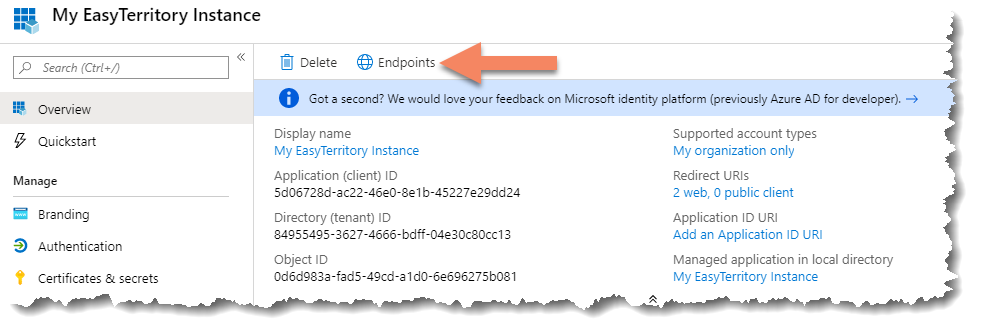
- Copy the OAuth endpoint. Note: You’ll only need the part of the UI in bold. https://login.microsoftonline.com/84955495-XXXX-XXXX-XXXX-04e12c34cc13/oauth2/token
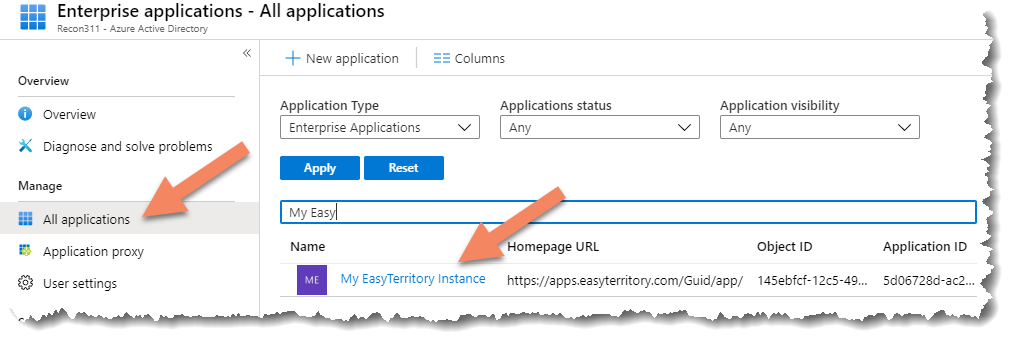
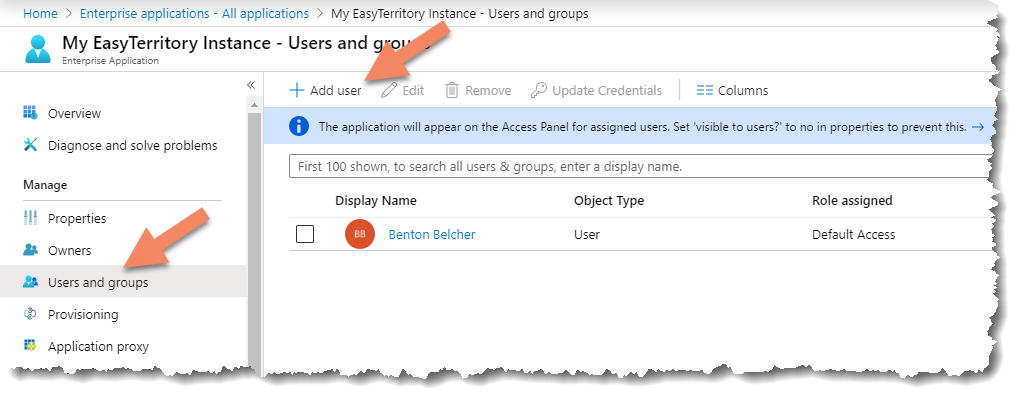
- Click ‘Azure Active Directory’ then click ‘Enterprise applications’.
- Find the EasyTerritory instance that was created and click it.
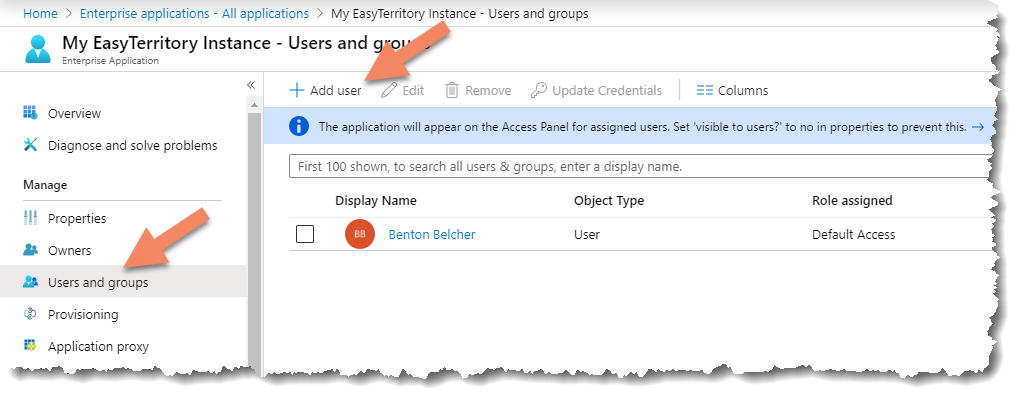
- Click ‘Users and groups’ then click ‘+ Add user’.
EasyTerritory Configuration Steps:
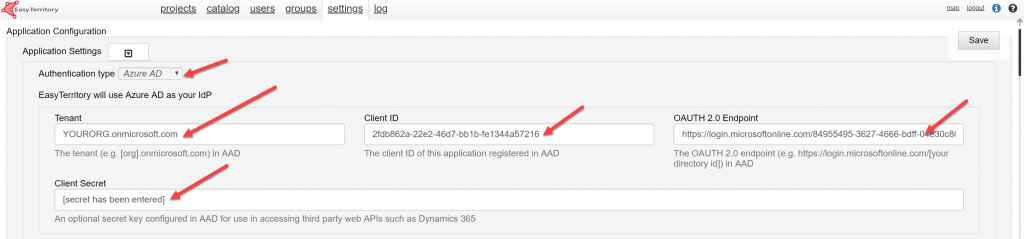
- With an EasyTerritory ‘Admin’ account into EasyTerritory go to the admin settings panel and set the following properties created in the steps above. https://apps.easyterritory.com/GUID/app/index.html#admin
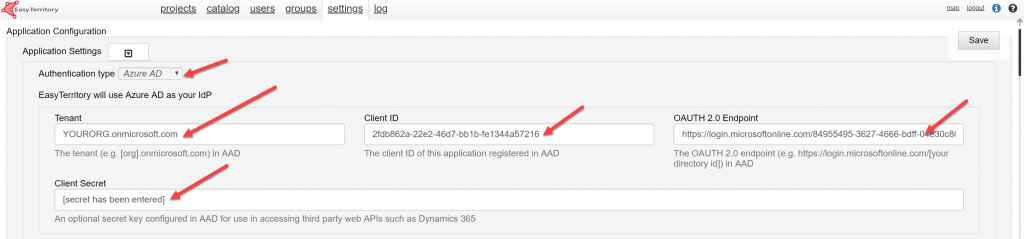
.
-
- Save the settings and open the EasyTerritory application in a new browser session to test.
- By default, EasyTerritory with Azure AD enabled, we’ll redirect to the IDP sign-on page in the browser. If you would like to embed EasyTerritory with a dashboard using an iFRAME in Dynamics 365, you’ll need to append this querystring property onto the iFRAME URL ?useAdalPopup=true.For example, https://apps.easyterritory.com/{YOUR GUID}/APP/index.html?projectId={YOUR PROJECT GUID}&useAdalPopup=trueIf you run into any issues setting up Azure AD, please email support@easyterritory.com.